As organizations more and more search to help and safe extra distant community connections, many are rethinking the normal VPN. Many VPN options exist to assist safe distant entry — mesh VPNs chief amongst them.
Mesh digital personal networks (VPNs) use a peer-to-peer structure that may theoretically be inexpensive than conventional VPN approaches. VPNs, that are estimated for use by 1.6 billion individuals, don’t carry the identical weight they used to within the safety stack, given huge safety holes, port shadow weaknesses, and broad consensus on their susceptibility to cyberattacks.
Nonetheless, the worldwide VPN market is strong — and anticipated to nearly triple by 2030 to $137 billion.
In legacy community stacks a VPN was used to entry network-based sources corresponding to on-prem line of enterprise apps and file shares as in the event you had been on the company community. In conventional enterprise networks in the event you had been inside the community perimeter you had inherent network-level entry to most every part on the community. Hybrid networks and a push towards zero-trust ideas have the trade shifting away from this mind-set, making the idea of a community perimeter much less of a focus relating to securing enterprises. When you’re operating a standard hub-and-spoke VPN structure, making the swap to mesh VPN may be value contemplating.
Why mesh VPN
Mesh VPN is a comparatively new idea that’s rapidly gaining momentum as extra distributors convey their companies to market. At its core, mesh VPN solves just a few weaknesses within the conventional VPN strategy and essentially integrates tightly with present safety stacks.
Diminished assault floor
Not like a client-server VPN with a hub-and-spoke mannequin, there isn’t any VPN server on the perimeter as a possible assault floor. Conventional VPN servers are incessantly simple to determine as there are a finite variety of VPN requirements and even proprietary protocols. This makes discovery a cinch and assault a pure development for dangerous actors. Conversely, members of a mesh VPN can reside behind a company firewall, on a house community, or on a mobile connection, behind NAT and different technical elements that incessantly trigger problem with VPNs. The power for nodes to attach to one another comes from a management aircraft that’s sometimes managed and maintained by the VPN vendor.
Higher help for Edge gadgets
Conventional VPNs primarily are available two flavors: site-to-site and distant entry. With present networks extending to edge gadgets tasked with enabling enterprise operations many edge deployments require both a software program VPN consumer or a community equipment configured with a site-to-site VPN connection. Mesh VPNs can definitely leverage a software program VPN consumer on all the well-liked working techniques however will also be applied straight into containerized purposes and different cutting-edge deployments that might not be an amazing match for conventional VPNs.
Targeted entry to networked companies
Mesh VPNs by default solely present entry to different members of the mesh VPN, to not your complete community. This might embrace servers, workstations, storage gadgets, cloud-based sources, and even software containers. This functionality can typically be additional refined to offer entry solely to the gadgets and companies acceptable for a specific person: that means whereas quite a lot of techniques and companies are accessible on the mesh VPN, particular person customers solely have entry to the companies to which they’ve a enterprise want for entry. The web results of these capabilities is basically dynamic firewall guidelines between nodes based mostly on the person’s roles and enterprise necessities. From a administration perspective, nodes and companies will be grouped and restricted utilizing ideas which can be acquainted to cloud directors corresponding to useful resource tagging and entry management lists.
Automated administration
Most mesh VPN options additional improve these ideas by providing API-based administration, that means the method of assigning roles and entry will be built-in with different administration and orchestration instruments already being leveraged inside the group. This may very well be within the type of an prolonged detection and response (XDR) answer, or just script-based automation that interacts with enterprise techniques.
Integration with current safety instruments
Mesh VPN options are constructed from the bottom up for hybrid work. As such, safety staples like identification administration (IDM) and cell gadget administration (MDM) assist kind a cohesive basis for the hybrid workforce. Integration with IDM helps streamline onboarding (and maybe extra importantly offboarding), in addition to dynamic modifications to system entry based mostly on modifications to person identities. Mesh VPN options make sense in safety gadgets alongside MDM as buyer laptops, tablets, and even cell phones can doubtlessly be added as VPN nodes.
Earlier than you leap
For a mesh VPN service to achieve success within the enterprise there are some non-negotiables. Integration with present authentication companies is an absolute should, and this extends to authenticating gadgets and making certain they meet gadget administration insurance policies. Moreover, integration with current instruments within the safety stack corresponding to occasion monitoring and EDR (endpoint detection and response) goes to be a tough requirement for gadgets accessing protected companies.
Why not mesh VPN
Mesh VPN options verify lots of containers, however as at all times there’s a flip facet of the coin. Companies nonetheless working in additional of an old-school, on-prem structure will probably have higher choices for a few causes.
Structure
Companies nonetheless functioning with the idea of a tough community perimeter and little to no cloud presence could not garner a lot worth from the hybrid identification and zero-trust capabilities which mesh VPN might help introduce. Likewise, if enterprise sources (corresponding to file servers or line of enterprise apps) are primarily contained inside the community perimeter a centralized VPN server stands out as the higher funding.
Value
Talking of investments, one doubtlessly main draw back to mesh VPN options comes right down to subscription prices. Most mesh VPN choices have a month-to-month subscription value per person, which may add up rapidly, notably for a number of the extra premium capabilities. As increasingly more legacy VPN options pivot to subscription-based licensing this concern have to be weighed rigorously.
Methods to: Assist connectivity to centralized company sources
VPNs have been used as a method to enable distant customers to entry sources inside the perimeter of the company community. Mesh VPNs are designed as a peer-to-peer community, that means the scope of the community extends by default solely to these gadgets with the VPN consumer put in. This turns into a little bit of a problem when making an attempt to offer entry to purposes or companies in a centralized location. Do you put in the VPN consumer on every server? How do you help workloads which can be clustered throughout a number of servers, or run in a stack like containerized apps? What about gadgets that merely don’t help software program set up, corresponding to industrial {hardware} and even printers?
Tailscale provides the idea of subnet routers to perform as a gateway to a number of gadgets on a community section. This function permits customers to put in the Tailscale consumer on a single laptop inside a community, and configure it to offer connectivity to different gadgets on that community. The method to allow a subnet router in Tailscale requires two steps for safety functions. First, you have to configure the Tailscale node as a subnet router, which on Home windows entails beginning Tailscale from the command line utilizing the --advertise-routes parameter adopted by IPv4 subnets outlined in CIDR notation. For instance, the next command serves your complete 192.168.1.x Class C subnet to the Tailscale community (the tailnet).
tailscale up --advertise-routes=192.168.1.0/24
Particular person endpoints will be shared by specifying the total IP tackle adopted by the /32 CIDR subnet masks. A number of subnets (or endpoints) will be outlined by separating them with a comma.
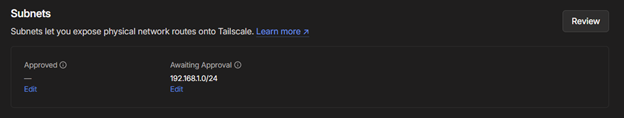
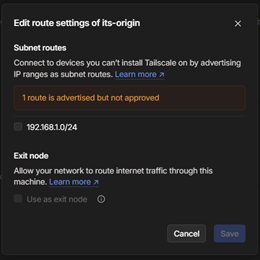
The second step to allow a subnet router entails utilizing the Tailscale admin console to allow particular person routes.
Tim Ferrill
Tim Ferrill
As soon as the route is authorised within the admin console, tailnet members will be capable to entry the purposes and companies on the goal subnet.
Methods to: Prohibit entry to sources and companies to licensed customers
In a zero-trust world entry to company sources must be restricted to the minimal variety of customers required. With the ability to entry the company community by a VPN mustn’t mechanically grant entry to internet servers or file shares, even on the community degree. Tailscale provides instruments to restrict what gadgets and customers can attain community sources utilizing entry management lists (ACLs).
ACLs in Tailscale boil right down to a supply and a vacation spot. Not like conventional firewall guidelines, Tailscale ACLs at all times lead to an ‘enable’ motion; connectivity is just allowed in the event you explicitly outline a rule. Throughout the Tailscale ACL coverage editor, you’ll be able to leverage customers or gadgets in bulk utilizing teams or tags respectively, or individually utilizing host or usernames. Entry to gadgets or subnets made accessible to the Tailnet utilizing subnet routing will also be allowed by referencing the subnet within the vacation spot portion of the rule:
{
"motion": "settle for",
"src": ["tag:mobile"],
"dst": ["192.168.1.0/24:80,139,443,445"],
},
This rule states that gadgets with the cell tag are allowed to hook up with gadgets on the 192.168.1.0/24 subnet, however solely on ports 80, 139, 443, and 445. Asterisks can be utilized as wildcards for each supply and vacation spot, both for the host or the allowed ports.
Methods to: Route web visitors from distant shoppers by a central community
One widespread VPN use case is to guard delicate web visitors whereas gadgets are related to public networks. Some industries require web visitors to be monitored and/or filtered. There are a number of methods to realize these necessities, however having all visitors routed by a central community has the potential to streamline the method. Tailscale’s exit node function facilitates assembly these wants.
Exit nodes are configured equally to subnet routing. The choice is enabled within the Tailscale consumer on the gadget designated because the exit node, after which the configuration is authorised by an admin within the admin console. Exit nodes will be configured as beneficial (also referred to as instructed) or obligatory, which permits Tailscale to both choose an exit node based mostly on latency or efficiency or to drive cell customers to ship all visitors by a single exit node. Obligatory exit nodes require Tailscale’s premium or enterprise plan, in addition to an MDM answer.
Methods to: Leverage company DNS servers for Tailscale shoppers
By default, Tailscale makes use of a function termed ‘Magic DNS’ to offer title decision to tailnet members. This title decision doesn’t lengthen to gadgets served on subnets and might show problematic when making an attempt to entry companies predicated on DNS corresponding to Energetic Listing.
Tailscale provides, nevertheless, the flexibility to outline a number of inner DNS servers to make use of for title decision. These DNS server entries will be configured for break up DNS, offering the flexibility to solely ahead requests for a selected area to the inner DNS server. Combining break up DNS with subnet routing and ACLs presents a compelling mix of performance.
Methods to: Obtain separation of duties inside Tailscale
Making a full-featured VPN answer is nice and all, but it surely’s not the tip of the story in trendy IT safety and compliance necessities. Separation of duties is a key greatest apply and a frequent part of compliance checklists. Tailscale provides a number of built-in roles you’ll be able to rapidly use to satisfy these enterprise wants:
- Community admins are the directors for the Tailscale account and have permissions to handle all facets of the community configuration. Consumer and gadget settings are will be seen by community admins, however they’re unable to make modifications even to their very own gadgets
- IT admins are much less targeted on the networking facets of the Tailscale account and extra on customers and gadgets. IT admins can view community particulars, together with ACLs contained within the tailnet coverage file, however can not make any modifications.
- Billing admins can handle pricing plans and billing info. They do have view entry to all facets of the admin console, however can not make modifications to networks, gadgets, or customers.
- Auditors have learn entry to all facets of the admin console, however no capability to make modifications. This function is especially helpful for compliance or audit causes, and even high quality assurance.
- Members have user-level entry to tailnet. They haven’t any entry to the admin console however can hook up with your tailnet and gadgets as allowed by ACLs.
Two extra roles, proprietor and admins, have full entry to all facets of the admin console. There can solely be one proprietor, and so as to delete that account the proprietor function should first be transferred.









