A phishing train carried out by the IT division of the College of California Santa Cruz (UCSC) has backfired, after inflicting pointless panic amongst college students and workers.
On the morning of Sunday August 18 2024, an electronic mail was despatched out by the College’s IT workforce in what its Scholar Well being Heart described as an try and “remind the campus neighborhood about finest cybersecurity practices and assist stop future phishing makes an attempt”.
Nevertheless, the e-mail didn’t describe how workers and college students may higher defend their on-line accounts by, say, adopting sturdy and distinctive passwords or enabling multi-factor authentication.
As a substitute, it falsely claimed {that a} workers member had examined constructive with the Ebola virus, after coming back from a visit to South Africa.
The e-mail, which had the topic line “Emergency Notification: Ebola Virus Case on Campus,” learn as follows:
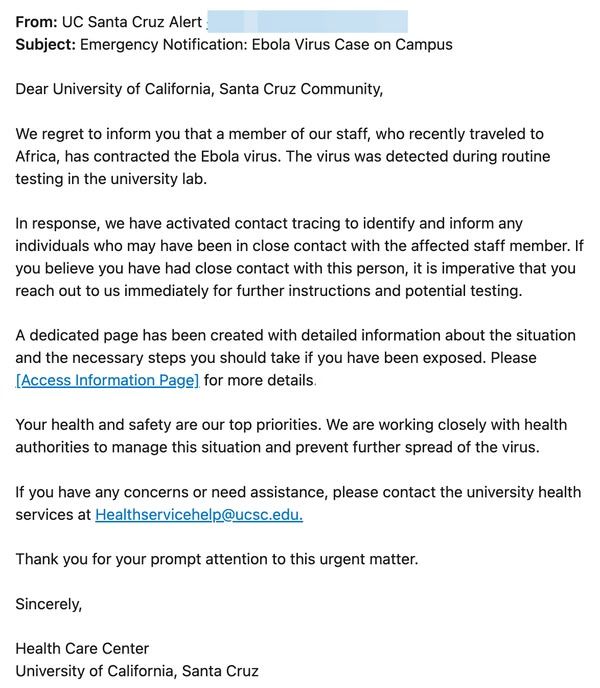
Throughout the electronic mail, people had been suggested that if they’d been in shut contact with the (unnamed) affected workers member it was “crucial” they take speedy motion, and click on on a hyperlink to a webpage the place extra info – it claimed – had been posted.
In fact, the e-mail’s declare that Ebola virus has been detected on campus was false, and anybody clicking on the hyperlink within the electronic mail was in actuality liable to handing over their login credentials to cybercriminals.
Though on this case the e-mail wasn’t a phishing marketing campaign perpetrated by on-line crooks, however as an alternative a “phishing check” orchestrated by UCSC’s IT division based mostly upon an actual phishing electronic mail it had noticed a couple of weeks earlier than.
Brian Corridor, UCSC’s chief info safety officer, apologised for the incident, acknowledging that phishing simulation electronic mail was “not true and inappropriate” and that it doubtlessly undermined belief in public well being alerts.
Phishing simulation checks like this are meant to assist individuals recognise and keep away from actual phishing makes an attempt. However, Corridor mentioned that he realised “the subject chosen for this simulation brought about concern and inadvertently perpetuated dangerous details about South Africa.”
The reality is that scammers can use very soiled tips to idiot unsuspecting customers into clicking on harmful hyperlinks, and haven’t any qualms about utilizing underhand strategies to socially engineer their victims into handing over their delicate credentials.
So it is comprehensible that some IT departments would possibly really feel very tempted to duplicate these strategies when operating a marketing campaign to check how nicely customers’ are defending themselves from falling for phishing assaults.
UCSC’s IT division has, like different organisations earlier than it, learnt the arduous method that not each try to boost safety consciousness shall be nicely obtained.









